I love honeypots and wanted to give opencanary a shot cause I kept hearing how cool it was. It’s written in python, and very easy to configure and extend.
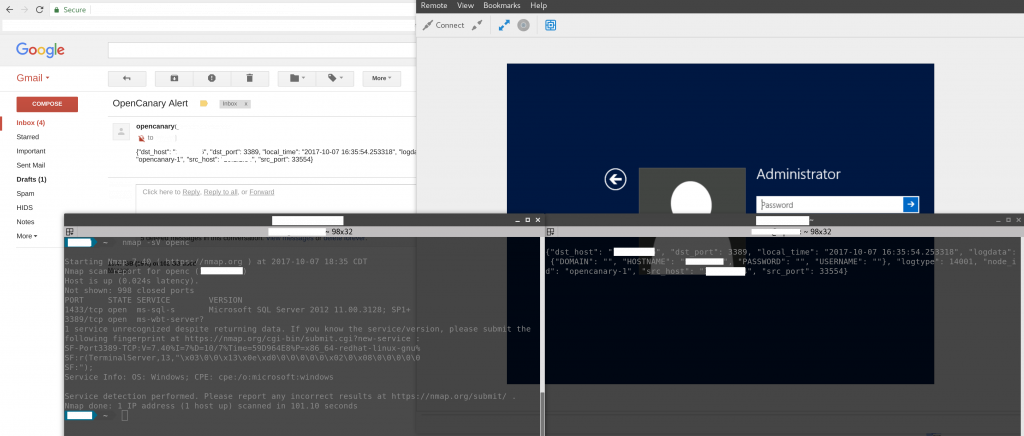
The idea is to stick these in various places in your network with fake services similar to what’s around it. In this case, I have opencanary acting like a Windows system running RDP and MSSQL.
Running on Debian 8.9
sudo apt-get install python-dev python-pip python-virtualenv build-essential libssl-dev libffi-dev python-dev virtualenv env/ . env/bin/activate pip install opencanary pip install scapy pcapy
Start the virtual environment and install rdpy
virtualenv env/ . env/bin/activate pip install rdpy
Copy the config and start it.
/root/venv/bin/opencanaryd --copyconfig opencanaryd --start
I edited the config, and disabled everything but MSSQL and RDP. Then I added a section under the PyLogger class handlers so that I could get emails forwarded to me. And I just put my email address in that users .forward.
},
"SMTP": {
"class": "logging.handlers.SMTPHandler",
"mailhost": ["localhost", 25],
"fromaddr": "opencanary@yourdomain.com",
"toaddrs" : ["someuser"],
"subject" : "OpenCanary Alert"
}
Then restarted the opencanary daemon.
opencanaryd --start
Nmap -sV shows it as running SQL Server 2012, and RDP. Any attempts to connect to or authenticate to these services are logged and emailed to me.
You can also setup SMS, logging to other systems, and implement your own services.
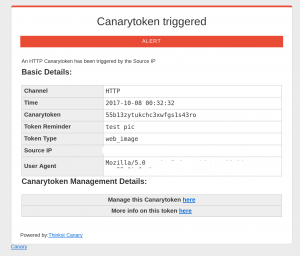
Something really cool is Canary tokens. You can create files, URLs, Email addresses, etc. and when they are used, you’ll get an out of band alert. Put a fake file on a share so an attacker steals it and opens it up, and you’ve got their IP address. Or stick some fake emails/domains in a database, and when they show up in a dump, receive emails or get queried, you’ll get an alert. Just little things that can help clue you in to what’s happening because it’s impossible to monitor for everything.
0 Comments